Application Delivery Controller aka ADC is an advanced version of server load balancing (SLB) which includes traditional load balancing along with some advance features such as health checks, SSL offloading, DDoS protection, Reverse Proxy, WAF etc.

History of Application Delivery Controller
Load balancing among several servers is not new. An initial version of load balancing was to have 1 to many relations between the domain name and IP addresses in DNS server. This severely lacked health checks as clients wouldn’t know if given IP is working or not. This drawback gave rise to next level of load balancing where a specific IP address was exposed to the world. This IP was catered by clustering software, which routed the traffic from clients to several servers in the backend.
Next generation load balancers introduced health monitors. If any of the servers goes unresponsive, the load balancer would stop sending traffic to that server until it was recovered. This also allowed system administrators to build some custom logic to add or reduce the servers in the farm based on the monitoring data.
ADCs are current generation load balancers which provide a variety of functions bundled together. Some of them are listed in the section below.
Features of ADC
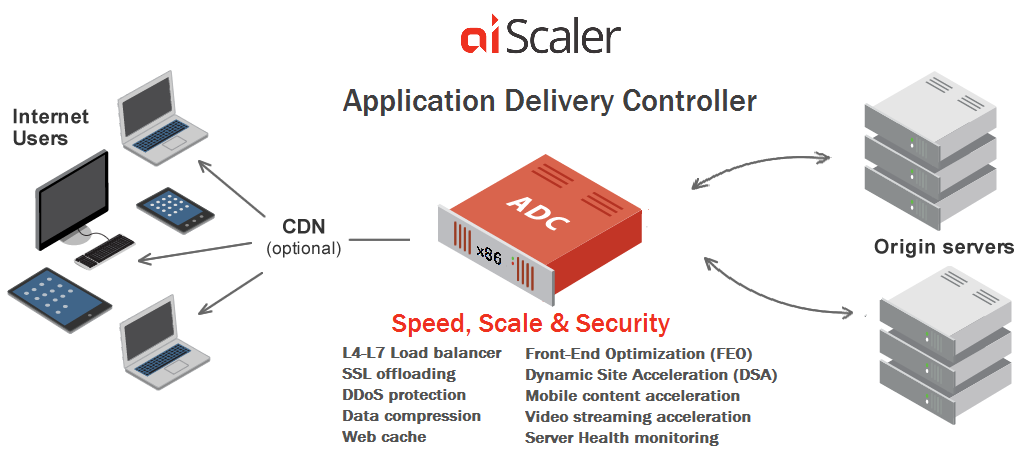
- SSL Offloading: ADC can handle the terminating SSL connection keeping the traffic between ADC and backend servers in plain text. And hence it helps in reducing the load on the application servers in the server farm.
- Multilayer load balancing: These load balancers can balance traffic at Layer 3/4 as well as Layer 7 of OSI model. Thus it gives an ability to route traffic based on IP addresses, subnets as well as based on the URL patterns, domains and HTTP header fields.
- Load balancing methods: ADCs can use various methods such as round robin, least packets, least bandwidth, latency or hashing of certain parameters.
- DDoS Protection: ADCs can look into the incoming traffic and detect DDoS before it starts loading the application servers, thereby defeating the attack.
- WAF: ADCs can have built-in Web Application Firewall which can prevent common security attacks such as Cross-site scripting XSS.
For a much more comprehensive list, you can to the article in related links section.
Related Links
Related Keywords
Load Balancer, Hardware, WAF, DAF